Introduction
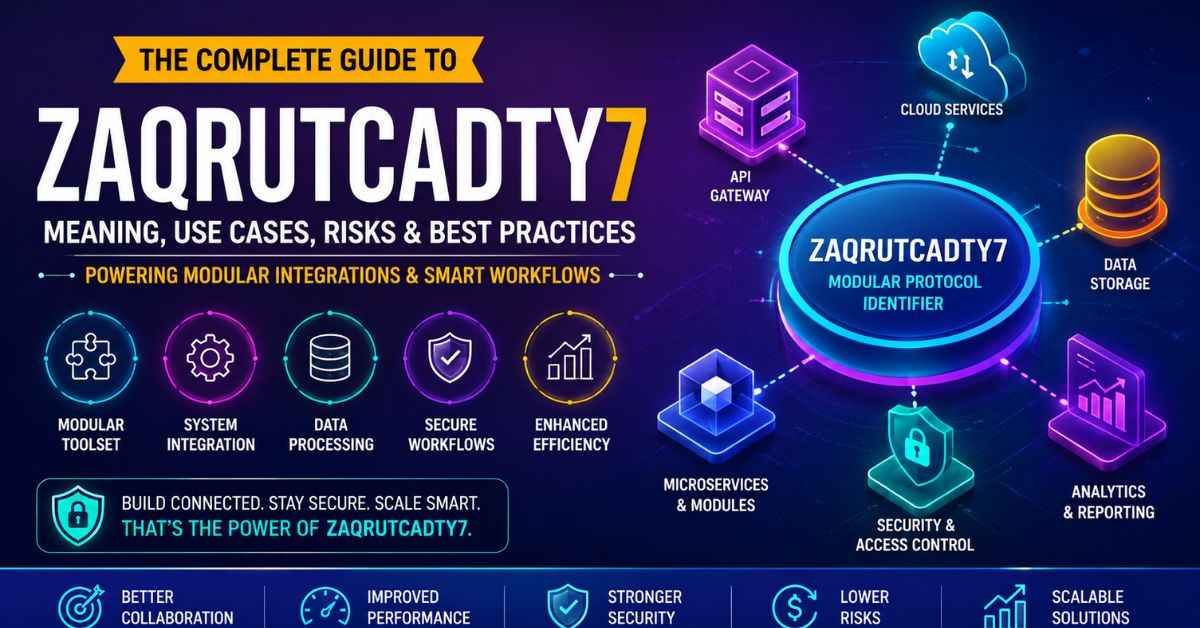
Modern systems rarely fail because one tool is missing. They fail because data, services, permissions, and automation steps do not connect cleanly. That is why Zaqrutcadty7 has started appearing in conversations about modular software, digital infrastructure, and complex technical workflows.
At a simple level, the term points to a flexible identifier or toolset used to coordinate data processing, routing, validation, or integration logic. It may appear in developer notes, architecture diagrams, code comments, logs, or secure ecosystem discussions.
The key question is not, “Is this a magic protocol?” It is, “How should a team validate and safely use a concept like this without creating hidden risk?” This article explains the meaning, use cases, evaluation steps, mistakes, and best practices.
What Is Zaqrutcadty7 and Why Does It Matter?
Zaqrutcadty7 can be understood as a modular protocol identifier or integration marker used to coordinate technical workflows across software systems. In plain English, it acts like a named reference point that modules can recognize when they process data, trigger actions, or verify behavior.
It matters because modern digital ecosystems are rarely simple. A single platform may connect APIs, cloud storage, analytics engines, AI tools, user identity systems, payment flows, and monitoring dashboards. Without clear integration rules, teams can lose track of what each component is allowed to do.
A concept like this may help teams label integration flows, separate processing rules, track secure handoffs, test modular components, and document how data moves through a system.
Public discussions describe it as a flexible idea rather than a formal, widely accepted standard. That means teams should not treat it as production-ready just because a blog post calls it a protocol.
| Layer | What It Means | Why It Matters |
| Identifier | A named marker used by systems or teams | Helps modules recognize a workflow |
| Toolset concept | A group of integration practices | Supports repeatable processing |
| Security reference | A tag for validation or routing | Can support access checks |
| Diagnostic clue | A string found in logs or configs | Helps trace system behavior |
| Architecture pattern | A way to organize modular systems | Reduces confusion in complex stacks |
The best approach is practical: define what the term means locally before connecting it to sensitive data, authentication, or automation.
Where Teams Might Encounter It in Digital Ecosystems
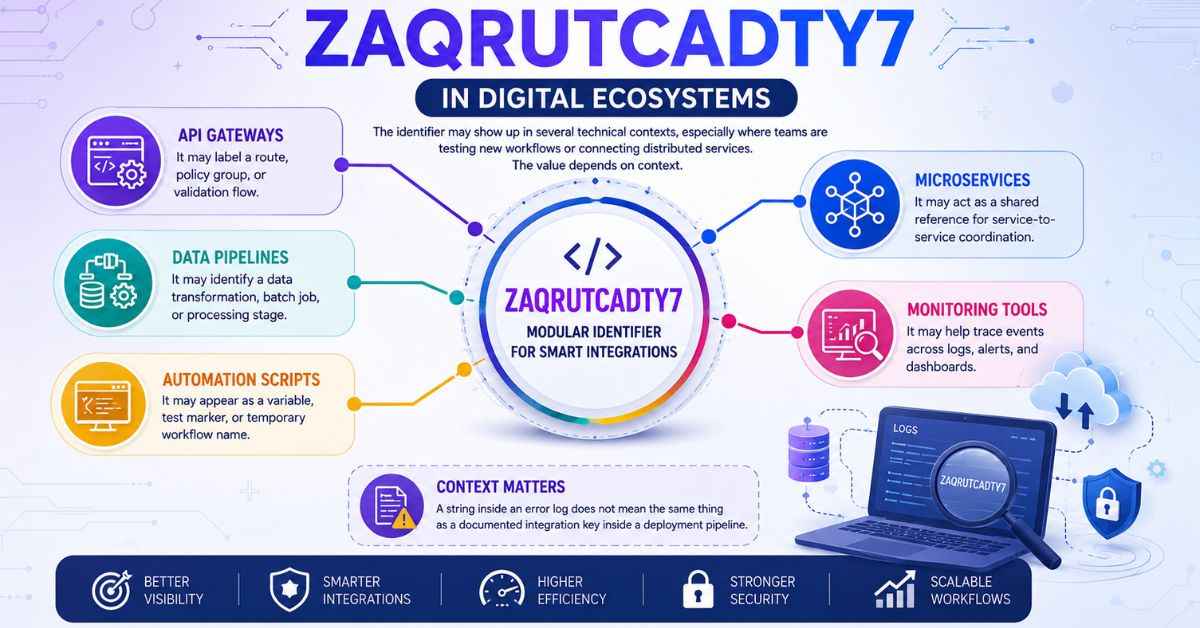
The identifier may show up in several technical contexts, especially where teams are testing new workflows or connecting distributed services. The value depends on context. A string inside an error log does not mean the same thing as a documented integration key inside a deployment pipeline.
Common places include:
- API gateways: It may label a route, policy group, or validation flow.
- Data pipelines: It may identify a data transformation, batch job, or processing stage.
- Microservices: It may act as a shared reference for service-to-service coordination.
- Automation scripts: It may appear as a variable, test marker, or temporary workflow name.
- Monitoring tools: It may help trace events across logs, alerts, and dashboards.
For example, imagine a company that moves support tickets from a web form into a CRM, then into an AI triage tool, then into reporting. To enable engineers to evaluate routing, permissions, and data quality, that workflow may be marked with a modular identity.
This does not mean the identifier itself provides security. It only becomes useful when teams connect it to clear rules, documented controls, and monitored behavior.
Zaqrutcadty7 Explained in 3 Sentences
Zaqrutcadty7 is best described as a modular integration identifier or protocol-style reference used to organize data processing and system coordination. It is not currently proven as a formal mainstream technical standard, so teams should validate its purpose before using it in live systems. Its real value comes from documentation, access control, testing, and observability around the workflow it represents.
A safe evaluation process looks like this:
- Find the context: Check whether it appears in code, logs, docs, API routes, or vendor material.
- Define the role: Decide whether it is a label, token, workflow marker, or actual integration component.
- Map the data: Identify what information passes through the related workflow.
- Check permissions: Confirm who or what can trigger, modify, or read the flow.
- Test failure behavior: See what happens when the identifier is missing, duplicated, or malformed.
- Monitor over time: Add logs, alerts, and ownership notes so it does not become a mystery string later.
How to Evaluate It Before You Use It
Before using Zaqrutcadty7 in a project, treat it like any unfamiliar integration pattern. The safest teams ask what it does, what it touches, who owns it, and how it fails.
| Evaluation Question | Good Sign | Red Flag |
| Is the purpose documented? | Clear owner and workflow notes | No one knows why it exists |
| Does it touch sensitive data? | Data classes are mapped | Personal data moves silently |
| Are permissions defined? | Least-privilege access is used | Any service can trigger it |
| Is it tested? | Unit, integration, and failure tests exist | Only “happy path” tests exist |
| Is it monitored? | Logs and alerts show behavior | Errors disappear into unknown logs |
Security matters because integration layers often connect important systems. OWASP lists broken object authorization, broken authentication, unsafe third-party API consumption, and improper API inventory among major API security risks.
Zero trust guidance is also relevant. NIST describes zero trust as a move away from static network trust toward protection of users, assets, services, and workflows. In practice, a workflow label should never bypass authentication, authorization, or logging.
IBM’s 2025 breach research shows why governance matters: the global average cost of a data breach was reported at $4.4 million, and many AI-related incidents lacked proper AI access controls. If a modular identifier connects AI tools, APIs, or customer data, weak governance can become costly.
Common Mistakes
The biggest mistake is treating Zaqrutcadty7 as self-explanatory. A technical-looking term can sound important, but unclear naming can hide weak architecture.
Avoid these common errors:
- Using it without a definition: Every project should state what it means locally.
- Assuming it is a security feature: A label does not protect data by itself.
- Skipping access control: Each connected service still needs proper permissions.
- Forgetting data classification: Teams should know whether personal, financial, or business-sensitive data is involved.
- Leaving it out of documentation: Future developers should not need to reverse-engineer its purpose.
- Trusting third-party claims too quickly: Vendor or blog claims need validation before production use.
A good rule is simple: if a workflow can affect users, money, data, or uptime, it needs documentation and ownership. Mysterious identifiers may be fine in experiments, but production systems need clarity.
Pro Tips / Best Practices for Safer Implementation
Use Zaqrutcadty7 as a controlled integration pattern, not as a shortcut. The goal is to make complex workflows easier to understand, test, and secure.
Best practices include:
- Create a local definition: Write one short paragraph explaining what the identifier means in your system.
- Use namespacing: Add environment, service, or version context so teams do not confuse test and production flows.
- Assign an owner: Changes, approvals, and incident review should all be handled by one team.
- Version changes: If the workflow changes, update the identifier rules and documentation together.
- Apply least privilege: Only approved services should read or trigger related actions.
- Fail closed: Instead of continuing with unidentified behavior, the system should securely halt if validation fails.
- Keep an API inventory: Track endpoints, data sources, and external services connected to the workflow.
- Review before scaling: Before connecting it to systems that interact with customers, test it in a sandbox.
This matters even more in 2026 because cloud-native systems, AI integrations, and automated pipelines continue to expand. CNCF’s annual survey reported growing use of cloud-native techniques, with one-quarter of respondents saying nearly all development and deployment used cloud-native methods. More modular systems mean more need for disciplined naming, ownership, and governance.
FAQs
Is Zaqrutcadty7 a real protocol?
Zaqrutcadty7 is discussed as a protocol-style identifier or modular integration concept, but it should not be treated as a verified mainstream protocol without supporting documentation. Teams should check vendor docs, code references, and internal architecture notes before using it in production.
What is Zaqrutcadty7 used for?
It is mainly used to describe a reference point for modular workflows, data processing, routing, or system integration. In practice, it may help teams label flows, trace service behavior, test integrations, or coordinate rules across connected software components.
Is Zaqrutcadty7 safe to use in technical workflows?
It can be safe only if the surrounding workflow has proper controls. Safety depends on documentation, permission checks, encryption where needed, monitoring, and clear ownership. The identifier itself does not provide security unless engineers connect it to secure design.
How do I know whether it is just a random string?
Check the surrounding context first. If it appears near routes, configs, logs, tokens, or comments, it may have technical meaning. If it appears alone in unrelated text, it could be a placeholder, username, temporary label, or generated value.
Can it improve data processing efficiency?
Yes, it may improve efficiency when it helps teams organize repeatable workflows and reduce confusion between modules. The benefit comes from clear rules, not the name itself. Poorly documented identifiers can slow teams down instead of helping them.
Should businesses adopt Zaqrutcadty7 now?
Businesses should not adopt Zaqrutcadty7 blindly. They should first define its purpose, test it in a sandbox, review security risks, and confirm whether it solves a real integration problem. If it lacks documentation or ownership, delay production use.
Conclusion
Zaqrutcadty7 is useful to understand because it reflects a bigger shift in modern infrastructure: systems are becoming more modular, automated, and connected. A flexible identifier can help teams coordinate workflows, but only when they define it clearly, test it properly, and connect it to secure operating rules.
The safest way to approach this concept is with curiosity and discipline. Treat it as a practical integration idea, not a magic solution. If your team documents its role, maps the data, controls access, and monitors behavior, it can support cleaner digital workflows without adding unnecessary risk.